A Simple Guide to NTFS Permissions vs. Share Permissions
What is the difference between NTFS permissions and Share Permissions?
How do they work together?
Read more on how to use them correctly!
Difference between NTFS Permissions and Share Permissions
Share permissions are applied when a shared folder is accessed over a network.
When you log into a local Windows machine (even if a file or folder is shared to other users within your network), and you access an object locally, NTFS permissions apply and share permissions do not apply.
In other words, NTFS permissions are applied to users who are logged into the network locally while share permissions are not applied.
It does not matter how restrictive share permissions have been set up on your network, if you have access to the object and you are logged into the workstation or server that “owns” the file or folder, you will be granted access.
Combining NTFS Permissions and Share Permissions
When using share permissions and folder permissions, please keep in mind, you can apply different NTFS permissions to each folder within a shared folder. Working this way will ensure a permission strategy for each kind of data located in an appropriate folder structure.
A frequently asked question when managing Windows Server environments is:
Once you combine share permissions with NTFS permissions, how do these two types of permissions work together?
The answer is rather simple and helps you to determine the most effective form of permission for a shared folder.
Both sets of permissions get applied, and the more restrictive of the two takes precedent.
To give you a better idea, take a look at the example below.
You give “Full Control” NTFS permissions to the “FileShare-Operatoren” group for a folder called MyFolder, as seen in the image below:
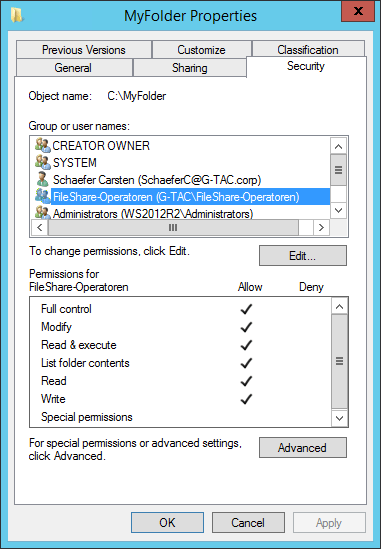
Full Control Permissions granted for MyFolder
If you share MyFolder within the Windows Network to the “FileShare-Operatoren” group using “Read” permissions and a user that belongs to this group tries to access the folder from the network, that user will only have “Read” access and not “Full Control”.
However, if that user then goes to the workstation or server where MyFolder is allocated, he will be granted “Full Control” permissions.
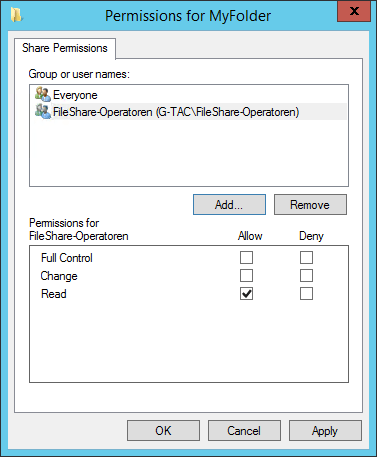
Read Only Share Permissions granted for MyFolder
3 Examples of Combining Share Permissions with Folder Permissions
In the next two examples, we have shared folders on NTFS volumes. These shared folders contain subfolders that have also been assigned NTFS permissions.
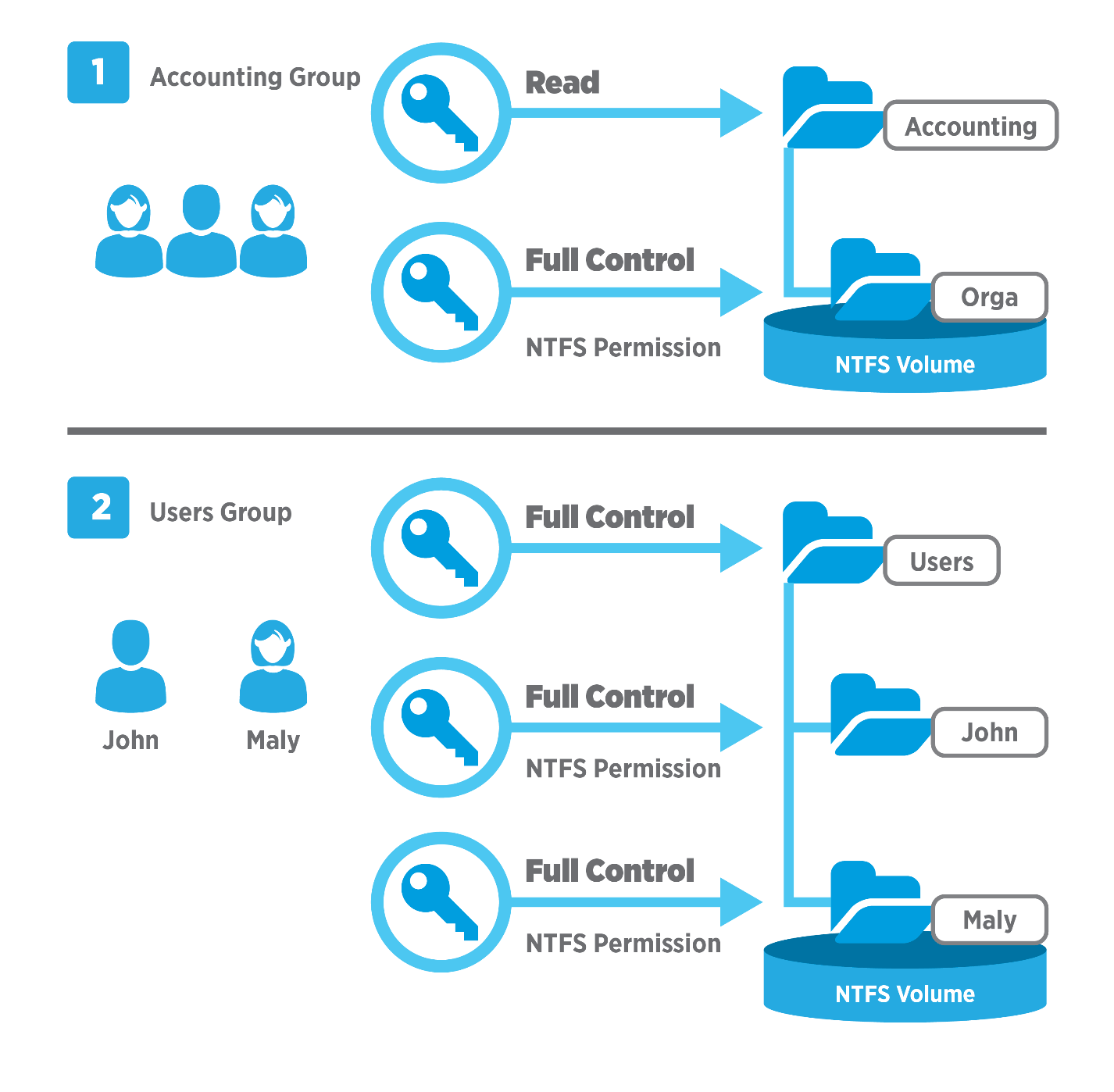
Combined Share and NTFS Permissions
First example:
- Accounting folder is shared.
- The Accounting group has the shared folder “Read” permission for this folder and the NTFS “Full Control” permission for the Orga subfolder.
The effective permissions for any member of the Accounting group for the subfolder called Orga is “Read”.
Second example:
- Users folder contains home folders for each user, here John and Maly.
- Both home folders contain data accessible only to the user for whom the folder is named.
- The Users folder has been shared and the Users group has “Full Control” permission for the Users folder.
- John and Maly have the NTFS “Full Control” permission for their home folder only and no NTFS permissions for other folders.
- Boths are members of the Users group.
The effective permissions for John and Maly for their own home folder is “Full Control”. But John has no access to Maly’s home folder and Maly has no access to John’s home folder.
Third example:
In this last example, the group Sales has these permissions, as seen in the image below:
- NTFS Permissions Full Control for shared folder Sales
- NTFS Permissions Read for File1
- NTFS Permissions Full Control for File 2
The effective permissions are:
- The members of this group are granted only Read access to File1 because it is the most restrictive permission.
- And they are granted Full Control to File2 because both permission assignments are at the same level.
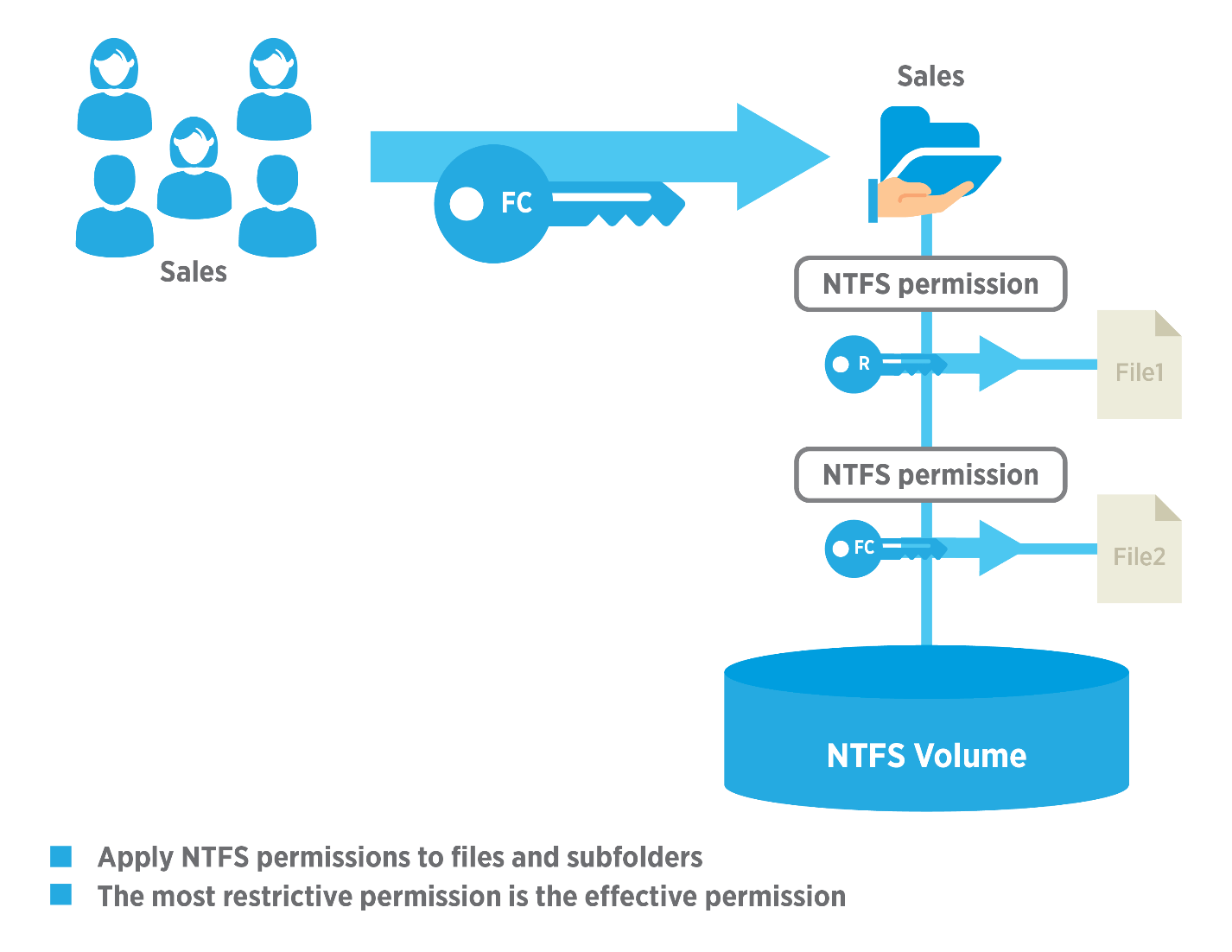
Effective NTFS Permissions
Best Practices For Working With Permissions
- It’s recommended to always share a folder by giving full access to a group made up of everyone, then control who can access that folder using NTFS permissions.
- Always try to share folders with groups instead of individuals, as this makes administration tasks far easier.
- To consolidate administration and group files into application, data, and home folders, you should centralize all home and public folders separately from your applications and operating system files. Doing so provides the following benefits: a) permissions may only be assigned to folders, not individual files and b) backing up will be less complex because you will not need to back up application files, as all home and public folders will be consolidated in one location.
- When you assign permissions for working with data or application folders, assign the “Read & Execute” permission to the Users group and Administrators group. This will prevent application files from being accidentally deleted or damaged by users or viruses.
- Always assign the most restrictive permissions that still allow users to perform required tasks. For example, if users only need to read information in a folder and should never delete or create files, assign the “Read” permission.
- Organize your resources so that folders with the same security requirements are located within one folder. For example, if users require “Read” permission for several application folders, store those folders within a single folder. This will allow you to share that larger folder instead of sharing each individual application folder.
- Use intuitive share names so that users can easily recognize and locate resources. For example, for the Application folder, use “Apps” as the share name. You should only use share names that can be used across all clients operating systems.
Have you assigned the correct NTFS permissions?
Feel good about your data security for all departments, managers, and other users, and get your free trial of the easiest and fastest NTFS Permission Reporter now!


Leave a Reply
Want to join the discussion?Feel free to contribute!